

Indian Journal of Science and Technology
DOI: 10.17485/IJST/v16i32.1240
Year: 2023, Volume: 16, Issue: 32, Pages: 2574-2579
Original Article
J Viji Gripsy1,2*, A Jayanthiladevi3, N Mahendiran4, A Sheela Rini5
1Post- Doctoral Research Fellow, Institute of Computer Science and Information Science, Srinivas University, Mangalore, Karnataka, India
2Associate Professor, Department of Computer Science, PSGR Krishnammal College for Women, Coimbatore, Tamilnadu, India
3Professor, Institute of Computer Science and Information Science, Srinivas University, Mangalore, Karnataka, India
4Assistant Professor, Department of Computer Science, Sri Ramakrishna College of Arts & Science, Coimbatore, Tamilnadu, India
5Assistant Professor, Department of Computer Science (PG), PSGR Krishnammal College for Women, Coimbatore, India
*Corresponding Author
Email: [email protected]
Received Date:22 May 2023, Accepted Date:16 July 2023, Published Date:29 August 2023
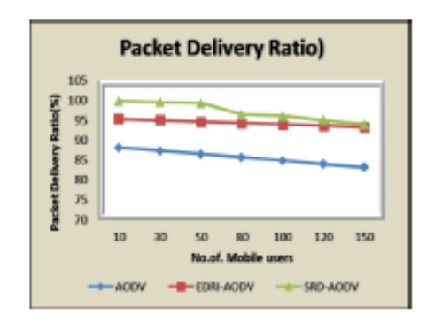
Objectives: To counteract grey hole and black hole attacks, the proposed method deploys a hybrid framework along with the Ad hoc on-demand distance vector (AODV) routing protocol. A modified protocol is called as SRDAODV (Secure Route Discovery-Adhoc On-Demand Distance Vector). Methods: The proposed work establishes secure route from secure node discovery, which protects from sequential attacks. The proposed framework has three significant components Node Authentication, Secure Neighbor discovery and route establishment, and Node Isolation system. Findings: Performance metrics like packet delivery ratio and delay are used to assess this protocol’s effectiveness. The SRD-AODV protocol contrasts with other active protocols as well as AODV. SRD-AODV has a PDR that is greater by 4.92% than EDRIAODV and 12.23% than AODV because it excludes network attacks, has flawless routes, and prevents packets drop or connections fail. This is because SRD-AODV has more perfect routes. The proposed SRD-AODV algorithm achieves 58.5% less E2E delay than AODV and 44.5% less than EDRI-AODV. Novelty: This protocol uses a variety of elements and techniques to establish efficient authentication using Elliptic Curve Diffie-Hellman algorithm (ECDHA) techniques, offering both proactive and reactive solutions. Additionally, this tries to secure the data packets and routing table information. Finally, it also aims to identify and stop incursions from sequential attacks in MANET.
Keywords: MANET; AODV; Black hole attack; Grey hole attack; Denial of Service
© 2023 Gripsy et al. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited. Published By Indian Society for Education and Environment (iSee)
Subscribe now for latest articles and news.