

Indian Journal of Science and Technology
Year: 2022, Volume: 15, Issue: 8, Pages: 318-325
Original Article
Krishan Kumar1, Mukesh Kumar Gupta2, Nishant Saxena2*, Vivek Jaglan3
1Department of Computer Science and Engineering, Suresh Gyan Vihar University, Jaipur, India
2Department of Electrical Engineering, Suresh Gyan Vihar University, Jaipur, India
3Department of Computer Science and Engineering,, DPG Institute of Technology and
Management, Gurgaon, India
*Corresponding Author
Email: [email protected]
Received Date:06 January 2022, Accepted Date:28 January 2022, Published Date:25 February 2022
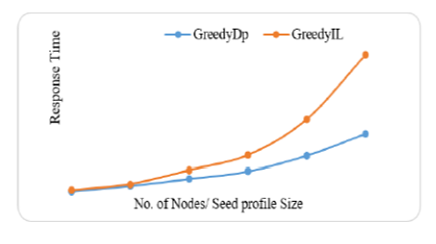
Objective: Privacy of user information in web search applications is traded off with quality of search results generated for a query by web search engine. In this article, we have developed a novel model utilizing Homomorphic Encryption for privacy protection of the user without compromising the quality of search results and response time. Methods: Response time is calculated using the GreedyDP and GreedyIL techniques, which is critical since encryption is usually followed by complicated calculations. Using the Homomorphic Encryption (HE) technique the user request is encrypted, rendering it unreadable or interpretable by eavesdroppers. Although the server will be unable to decode the requests, it will be possible to process those using algorithms and computations. The suggested model was utilized to evaluate the reaction time performance of four distinct current HE techniques. Findings: From the proposed model, it is inferred that, the performance of Gentry HE is superior to others since it takes 6% less time than its nearest competitor Paillier. Implementations show that the developed model, query encryption, does not create response delays and so supports the framework. Novelty: This research proposes a new PWS model with HE to increase data security and privacy in online search applications. The suggested study uses the GreedyDP and GreedyIL new methodologies.
Keywords: Personalised Web Search; user profile; Homomorphic Encryption; GreedyDP; GreedyIL
© 2022 Kumar et al. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited.
Published By Indian Society for Education and Environment (iSee)
Subscribe now for latest articles and news.