

Indian Journal of Science and Technology
DOI: 10.17485/IJST/v15i16.2042
Year: 2022, Volume: 15, Issue: 16, Pages: 750-759
Original Article
Humberto Troncoso Espinosa Fredy1*
1Department of Industrial Engineering, Faculty of Engineering, Universidad del BíoBío, Concepción, 4030000, Chile
*Corresponding Author
Email: [email protected]
Received Date:10 November 2020, Accepted Date:23 March 2022, Published Date:02 May 2022
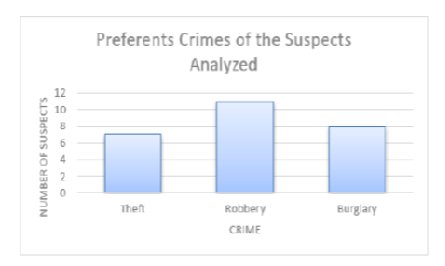
Background: The disarticulation of criminal organizations reduces the rates of victimization and insecurity in the population. One of the main characteristics of a criminal organization is the cohesion among its members. This investigation proposes a cohesion index that allows identifying quickly in Big databases individuals suspect to belong to criminal organizations and focus investigation resources on them. Methods: To obtain the index, we analyze the information provided by the Criminal Analysis and Investigative Focus System from the Regional Public Prosecutor’s Office in Biobío and the Investigation Police of Chile. Findings: The results show that the suspects with a higher cohesion index and a higher number of criminal cases commit crimes associated with criminal organizations.
Keywords: Criminal Cohesion; Crimes Against Property; Criminal Organization; Criminal Databases
© 2022 Fredy. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited.
Published By Indian Society for Education and Environment (iSee)
Subscribe now for latest articles and news.