

Indian Journal of Science and Technology
Year: 2023, Volume: 16, Issue: 14, Pages: 1045-1055
Original Article
M Y Shiju Thomas1,2*, V N Addapalli Krishna1, M Bindiya Varghese2
1Computer Science and Engineering, School of Engineering and Technology, Christ University, Bangalore, Karnataka, India
2Rajagiri College of Social Sciences (Autonomous), Kerala, India
*Corresponding Author
Email: [email protected]
Received Date:26 April 2022, Accepted Date:04 March 2023, Published Date:06 April 2023
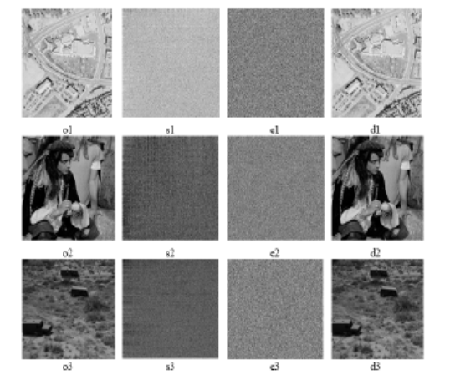
Objectives: To develop an efficient algorithm based on block-scrambling and chaotic maps to generate an encrypted image capable of protecting sensitive information. Methods: The proposed technique introduces the twopass Block-XOR operation column-wise and then swaps pixels within each block in an anti-clockwise crisscross pattern to separate and rearrange nearby pixels into distinct rows and columns. The strong correlations between nearby pixels are disrupted, making it challenging to identify the original image. Afterward, image diffusion using binarization is performed on the obtained scrambled image using a chaotic sequence generated by a logistic map. Findings: This scheme has accomplished an efficient encryption method based on block-scrambling and a chaotic map. The experimental results show that the system is competent for generating cipher text by encrypting images and can withstand malicious attacks and thus protect sensitive information. The histogram analysis results show that the proposed system displays adequate resistance to statistical attacks. The histogram of cipher text is uniformly distributed and bears no resemblance to the plaintext histogram. The differential analysis shows that the NPCR and UACI values are greater than 99 and 33, respectively, and are acceptable to conclude that the system is also resistant to differential attacks. The proposed technique experimented with using standard test images from the literature and the USC-SIPI image dataset. Novelty: A two-pass Block-XOR operation strengthens the scrambling by altering the value of the image pixel. Then an anti-clockwise crisscross pixel swapping algorithm is utilized for block scrambling.
Keywords: Cryptography; Chaotic Maps; Pixel Confusion; Histogram Analysis; Cyber Attacks
© 2023 Thomas et al. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited. Published By Indian Society for Education and Environment (iSee)
Subscribe now for latest articles and news.