

Indian Journal of Science and Technology
DOI: 10.17485/IJST/v16i36.2503
Year: 2023, Volume: 16, Issue: 36, Pages: 3002-3008
Original Article
Sunny Sall1*, Rajesh Bansode2
1Research Scholar, Department of Information Technology, Thakur College of Engineering and Technology, Mumbai, Maharashtra, India
2Professor, Department of Information Technology, Thakur College of Engineering and Technology, Mumbai, Maharashtra, India
*Corresponding Author
Email: [email protected]
Received Date:29 December 2022, Accepted Date:14 August 2023, Published Date:27 September 2023
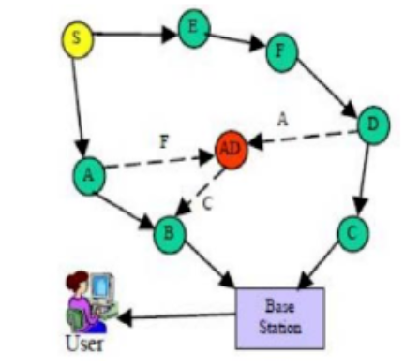
Objectives: To design and develop pairwise key generation techniques for malicious node detection in wireless sensor network. Method: The lightweight key generation method has been used for data encryption with the collaboration of the sender node, entry node and destination. The unique identity of the destination server has utilized for data encryption and decryption as a master key. The proposed method generates a concise key length that reduces encryption and decryption time. It also helps to detect the misbehaviour of internal nodes when it takes higher time for data decryption and transmission. Findings: The proposed system reduces end to end delay around 10%, the packet delivery ratio improves by 3.30%, throughput by 9.87, and energy consumption by 20.50% than Advanced Encryption Standard and Rivest Shamir Adleman algorithm. The proposed encryption algorithm compresses the cypher data, reducing the network overhead, and detecting malicious nodes, providing higher security from internal and external intruders. This simulation obtains better results than existing systems that enhance around 7-9% throughput with all QoS parameters. Novelty: The proposed system eliminates network overhead of key transmission to the destination. Using this approach, the sender node generates a lightweight key for data encryption using the destination node, which means only the destination node can decrypt the data using the generation of similar keys. When any random node tries to generate such keys, it violates time-bound, and system detects as a malicious node.
Keywords: Wireless Sensor Network; Intrusion Detection System; Energy Consumption and Conservation; Broadcast Tree Construction; Lightweight Key Encryption; Pairwise Key Generation
© 2023 Sall & Bansode. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited. Published By Indian Society for Education and Environment (iSee)
Subscribe now for latest articles and news.